In the “Cybersecurity: Endpoint Security” course, learners will embark on a comprehensive journey through cybersecurity fundamentals, providing a solid foundation to comprehend the prevailing threats, vulnerabilities, and risks in today’s digital environment. As learners progress, they will delve into the intricacies of various network protocol and service vulnerabilities, specifically focusing on Windows and Linux endpoints. This course immerses learners in current cybersecurity trends and potential attacks and equips you with effective mitigation and defense strategies to counter these threats. Whether one seeks to grasp essential concepts in endpoint operations and security or dive into the intricacies of malware analysis, this course will provide learners with the knowledge and skills necessary to navigate the cyber realm safely and confidently.
What You’ll Learn
Upon course completion, you will have a comprehensive grasp of cybersecurity, empowering you to recognize common threats and analyze typical attack patterns. This includes the ability to articulate threats, vulnerabilities, and attacks across various domains, recommend fundamental threat mitigation measures, utilize malware investigation tools to comprehend malware characteristics, and evaluate endpoint protection and the repercussions of malware.
Skills You’ll Gain
- Detecting intrusions
- Threat monitoring and analysis
Roles
- Cybersecurity Officer
- Network Administrator
Course Outline
Module 1: Introduction to Cybersecurity
Module 2: Cybersecurity Threats, Vulnerabilities, and Attacks
Module 3: Securing Networks
Module 4: Attacking the Foundation
Module 5: Attacking What We Do
Module 6: Wireless Network Communication Devices
Module 7: Network Security Infrastructure
Module 8: The Windows Operating System
Module 9: Linux Overview
Module 10: System and Endpoint Protection
Module 11: Cybersecurity Principles, Practices, and Processes
Required Resources
Computer, 2GB RAM or higher, 8GB free disk space (Hardware); Oracle VirtualBox, Packet Tracer 8.0.1 or higher (Software); High-speed Internet Connection (Network)
Pre-Requisites
PC and internet navigation skills, basic understanding of computer networks, and knowledge of TCP/IP networking including network protocols, services, and processes; completed course Cybersecurity: Network Defense
Assessment
In this Cybersecurity: Endpoint Security course there will be:
- One (1) diagnostic assessment will be conducted asynchronously and knowledge-based, allowing learners to proceed at their own pace. It offers the flexibility for remote or on-site participation.
- Two (2) formative assessments, one concentrating on knowledge and the other on performance-based skills measurement. Both formative assessments are to be conducted synchronously, allowing learners to participate remotely or on-site.
- A performance-based summative assessment conducted synchronously, offering learners the option of remote or on-site participation.
Credit and Recognition
The certification is globally recognized wherever Cisco and Cisco NetAcad are acknowledged.
This course is delivered in partnership with CISCO, a leading global technology company, through its CISCO Networking Academy Program. To ensure the quality of this microcredential, continuous feedback loops with students, instructors, and industry practitioners are maintained to improve content, delivery, and assessment methods continuously.
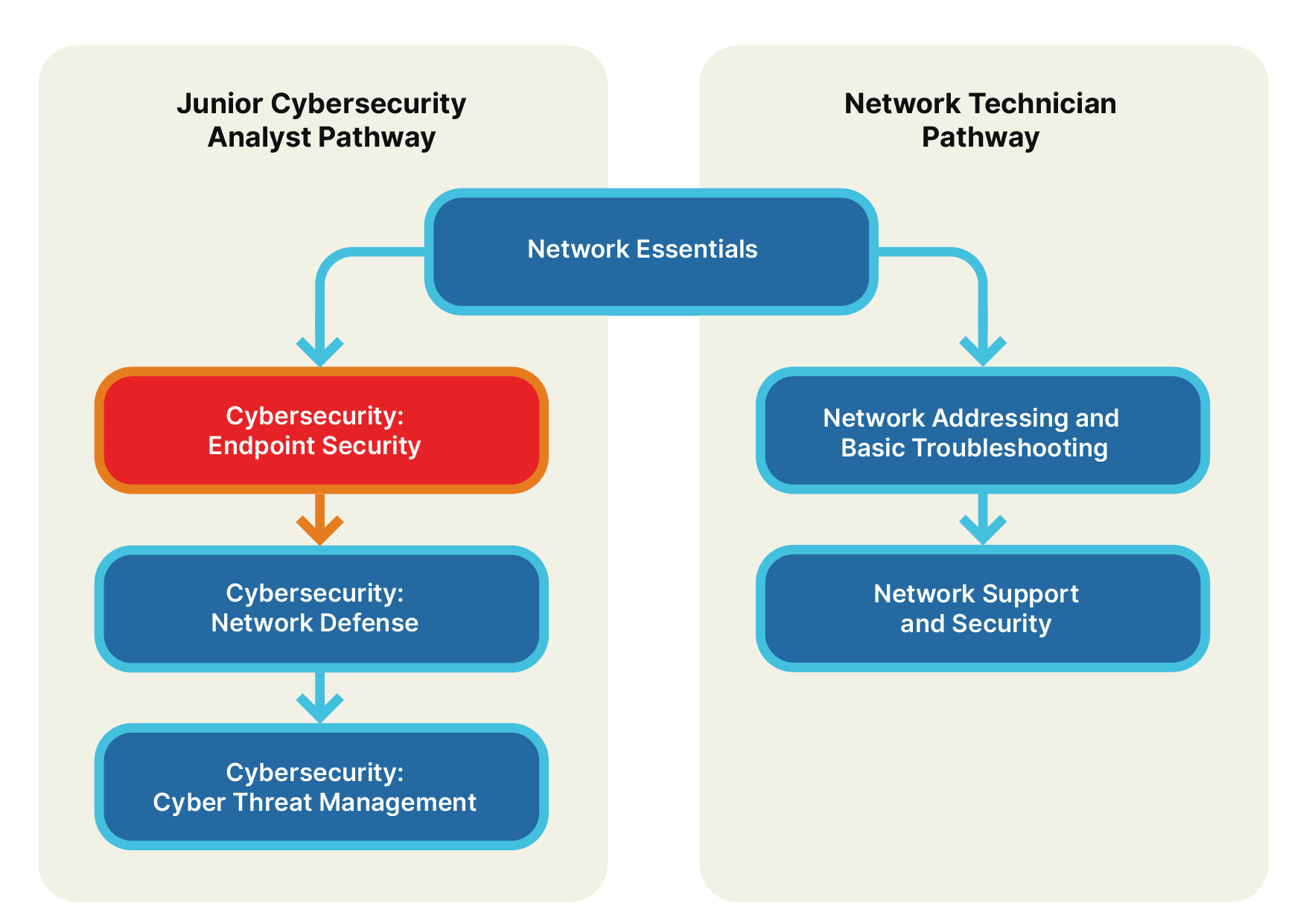
Learning Pathways
Learners are eligible to take the CISCO Certification “Cybersecurity: Network Defense.” Also
Cybersecurity: Endpoint Security
Networking Essentials is a prerequisite for Cybersecurity: Endpoint Security. Upon completing this course, you’ll be prepared to advance to the next step in the Junior Cybersecurity Analyst Pathway.